
Security Kit – Drupal module overview
Security Kit is a module that helps with eliminating the likelihood of exploiting security vulnerabilities on your website. Thanks to a multitude of features, such as Anti-XSS, Anti-CSRF, Anti-ClickJacking you can get yourself a peace of mind and comprehensively define a security policy for your website.
At our Drupal agency, we value the security of our customers' websites and make every effort to ensure that the solutions we provide are as bug-free as possible, which is why our development team uses tools to achieve this goal optimally. We use modules provided by Drupal's outstanding community, which facilitate this process. For example, when auditing an acquired project, we use the Hacked module, and while implementing the solutions required by your projects, we are always taking advantage of the Security Review. Today I would like to introduce you to another module that will help you secure your website – Security Kit (SecKit).
Dates
The first version of the module was released on 26 March 2011. The latest update was released on 28 August 2020. The module is now considered to be feature-complete by its developers – new features are currently not being developed, and the updates focus solely on patches.
Module popularity
The module is used by about 56,000 websites, including 25,000 based on Drupal 7 and 26,000 on Drupal 8.
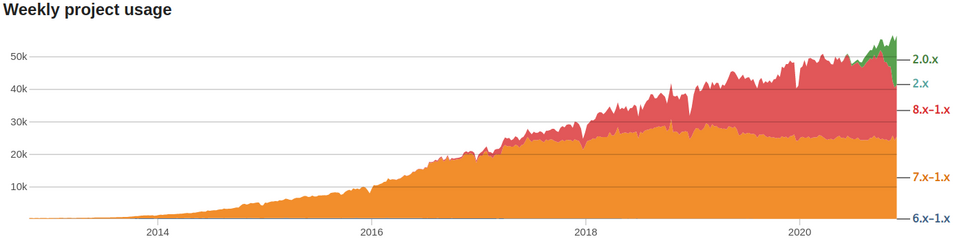
You can find detailed popularity statistics here.
Module developers
The module was developed by p0deje. It is currently maintained by Acquia and Catalyst IT. The vast majority of commits were provided by p0deje (141), jweowu (26) and mcdruid (24).
As of now, the module has four maintainers: mcdruid, jweowu, badjava, and p0deje.
What does it do?
Security Kit combined with Drupal offers additional options and features that improve security, reducing the risk of exploiting vulnerabilities on your website, by adding Anti-XSS, Anti-CSRF, Anti-ClickJacking, HSTS and CORS implementations. The module enables you to define a multitude of security policies – you can find a description of each configuration option in the "Settings" section.
Let's take a closer look at what it can do for you!
Anti-XSS
Features that help lower the possibility of exploiting cross-site scripting (XSS) vulnerabilities on your website. XSS is a type of website vulnerability that allows the attacker to execute any JavaScript code directly on the end device. XSS may result in leaking data, such as login and password, credit card details, user account information and much more. There are a number of types of XSS attacks; if you want to learn more, you can start exploring them here.
Anti-CSRF
Cross-Site Request Forgery (CSRF) is an attack type that allows the attacker to trick end users into performing specific actions on a website. A CSRF attack may, for example, result in the end-user losing their funds, changing their email address linked to the website, changing their password and any other action which the user can perform.
Anti-Clickjacking
Clickjacking is an exploit which enables an attacker to trick end users by displaying a concealed xframe, which the user can unwittingly click to run a given action on another website. Attacks of this kind can be used, for example, to farm likes on the attacker's Facebook page. The latter type of attack now even has its own name – Likejacking.
HSTS
HTTP Strict Transport Security (HSTS) security policy that minimises the risk of man-in-the-middle attacks, which entail modifying a request before it even reaches the server.
CORS
Cross-origin resource sharing (CORS) is a mechanism that allows you to specify a list of trusted domains from which the user can download resources on your website.
Unboxing
The module does not require any external libraries to work correctly. Security Kit can be installed in a standard manner, but – as always – we do recommend using composer:
composer requires drupal/seckit
Settings
Cross-site scripting
This section contains settings that boost your website's security performance in terms of XSS-type attacks.
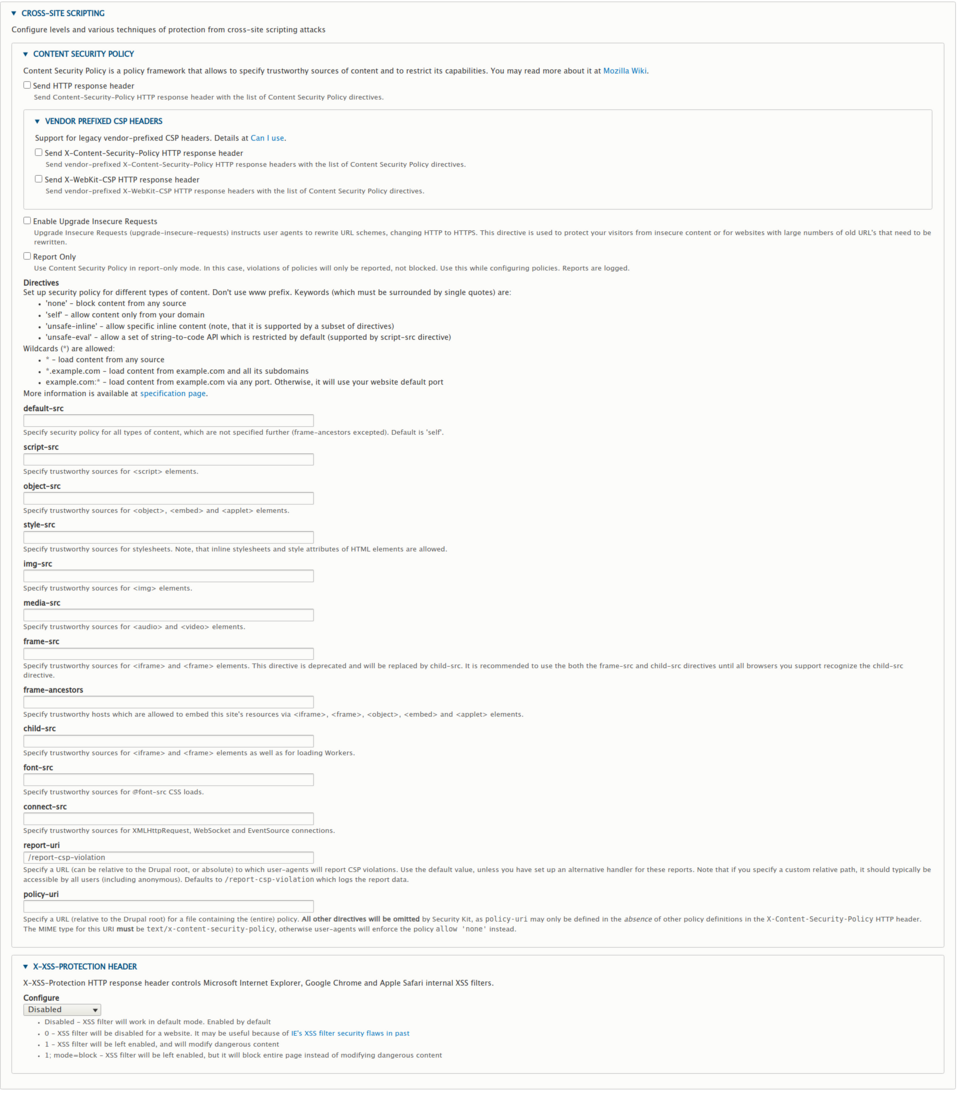
Content security policy
Security policy enables you to identify trusted content sources. Serving content from untrusted sources may lead to security issues, such as data leakage and malware distribution. You can read more about this here.
Send HTTP response header
If you select this option, the CSP policy is enabled.
Enable Upgrade Insecure Requests
If you select this option, all HTTP requests are redirected automatically to HTTPS.
Report only
If this option is selected, all the cases of content security policy breaches will not be blocked, only logged.
Default-src
This option defines a security policy for all content on the website, such as scripts, styles, images, media, frames, etc. If you do not specify a separate policy for a given content type, the CSP will use the policy specified in this field.
This allows you to provide trusted sources for particular content types, such as script, object, style, img, media, frame, font.
Report-uri
Path used for reporting requests violating your CSP policy.
Policy-uri
If you want your CSP policy to be saved in one file, here you can specify a path. If this field is filled, the settings per content type are omitted.
X-XSS-Protection header
Each browser has its own internal safeguards against XSS. X-XSS-Protection header enables you to disable the default anti-XSS protection built into your browser, run the safeguards along with modifying unsecured content to protect users from XSS attacks or run protection mechanisms that will block all dangerous content. If you would like to learn more about the header, take a look here.
CORS
This section contains settings that protect your website from cross-site request forgery attacks.
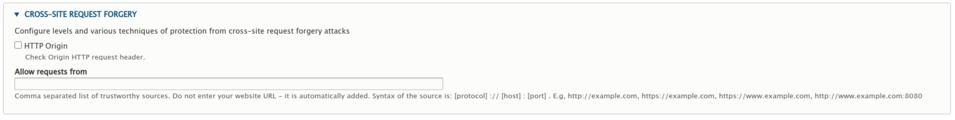
HTTP Origin
If you select this option, you enable the validation of the HTTP request source, thus enabling CORS protection.
Allow request from
A list of accepted requests.
ClickJacking
This section contains settings that improve your website's security in response to ClickJacking attacks.
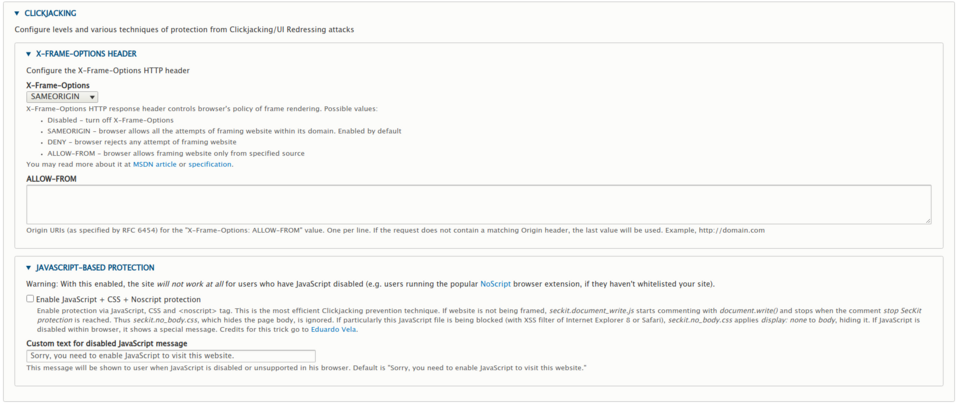
X Frame options
X-Frame-Options configuration
- Disabled - disables the X-Frame-Options header.
- SAMEORIGIN – makes it so that the page can display xframes only served from the same domain.
- DENY – locks all xframes.
- ALLOW-FROM – allows you to specify a list of domains with xframes enabled.
You can read more about the XFrame header here.
You can also find the header specification here.
JavaScript-based protection
Enables anti-clickjacking protection using JavaScript. This solution will not work for users who block JavaScript using browser plug-ins such as NoScript.
Custom text for disabled JavaScript message
Enables you to provide a message that will be shown to users blocking JavaScript on your website, as well as users whose browsers do not support JavaScript.
SSL/TLS
A section containing settings improving SSL/TLS security.
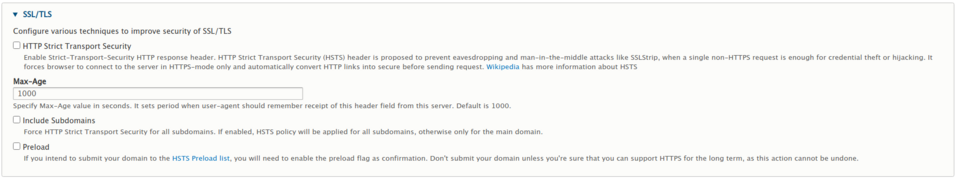
HTTP Strict Transport Security
Enables the Strict-Transport-Security (HSTS) header – enabling this option will increase security by reducing the risk of man-in-the-middle attacks such as SSLStrip. You can read up on HSTS here.
Max-Age
Defines the max-age value of the HSTS header. Max age is the number of seconds for which the website is treated as HSTS-enabled by the end-user.
Include Subdomains
Enables HSTS for all subdomains – by default, the HSTS header is only sent from the main domain.
Preload
Most popular browsers have HSTS preload lists with sites that are defined as HTTPS-enabled. If you want your domain to be added to the HSTS Preload list, you need to check this option.
Expect CT
Expect-CT header configuration options allow you to enable reporting and enforcing the Certificate Transparency policy. The Certificate Transparency Policy defines the sources, delivery and signing mechanisms of certificates when using TLS connections. You can read more about this here.
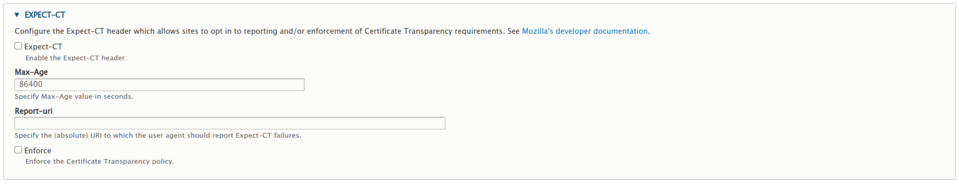
Expect-CT
Enables Expect-CT header.
Max-Age
Defines the max-age attribute for the Expect-CT header. Max age is the number of seconds after receiving the Expect-CT header during which the user's browser considers your website to be compliant with Expect-CT header.
Report-uri
URI for reporting Expect-CT errors. Errors are reported if the user does not receive correct CT information.
Enforce
The optional header parameter specifies whether the user should enforce the Certificate Transparency policy or only report in case of an error.
Feature policy
Configuration options for the Feature-Policy header, which determine the API configuration and behaviour, as well as features provided by the browser, for example, it allows you to limit the APIs used for interacting with user's camera or microphone, as well as change the default behaviour of the autoplay attribute on mobile devices. You can find out more about this here.
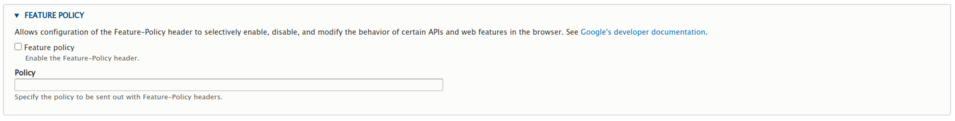
Feature policy
Checking this option enables the Feature-Policy header.
Policy
Defines the Feature-Policy header policy.
Miscellaneous
Configuration of the remaining module options that do not belong to any particular category.
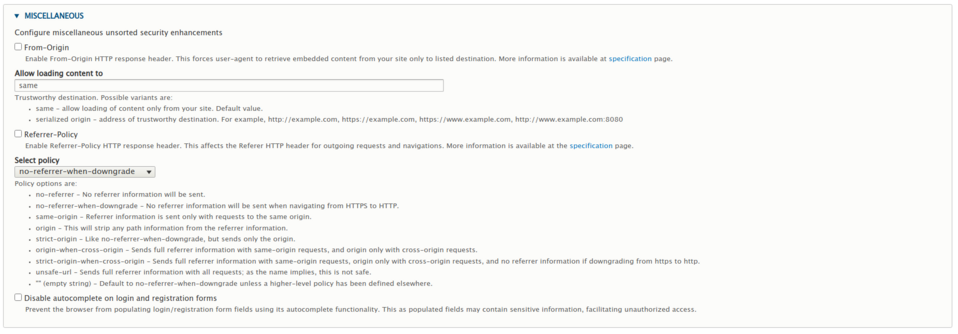
From-Origin
Enables the From-Origin-Response header. This option specifies websites on which the resources from your website can be embedded. You can find out more about this in the header specification.
Allow loading content to
Enables you to specify a list of domains, where your content can be embedded (if From-Origin is used).
Referrer-Policy
Enables the Referrer-Policy response header.
Select policy
Defines the policy for the Referrer-Policy header. Information about this header and available options can be found in the specification.
Disable autocomplete on login and registration form
Checking this option will disable the ability of the browser to fill in the login and registration forms automatically.
Conclusions
The presented module enables you to configure many options that increase the security level and performance of your website. It also provides you with a number of ways that allow you to define security policies, while the added security mechanisms help protect your website against popular attacks. Our Drupal developers recommend deploying the SecurityKit module.









